Should You Use Zoom or Not?
Should You Use Zoom or Not?
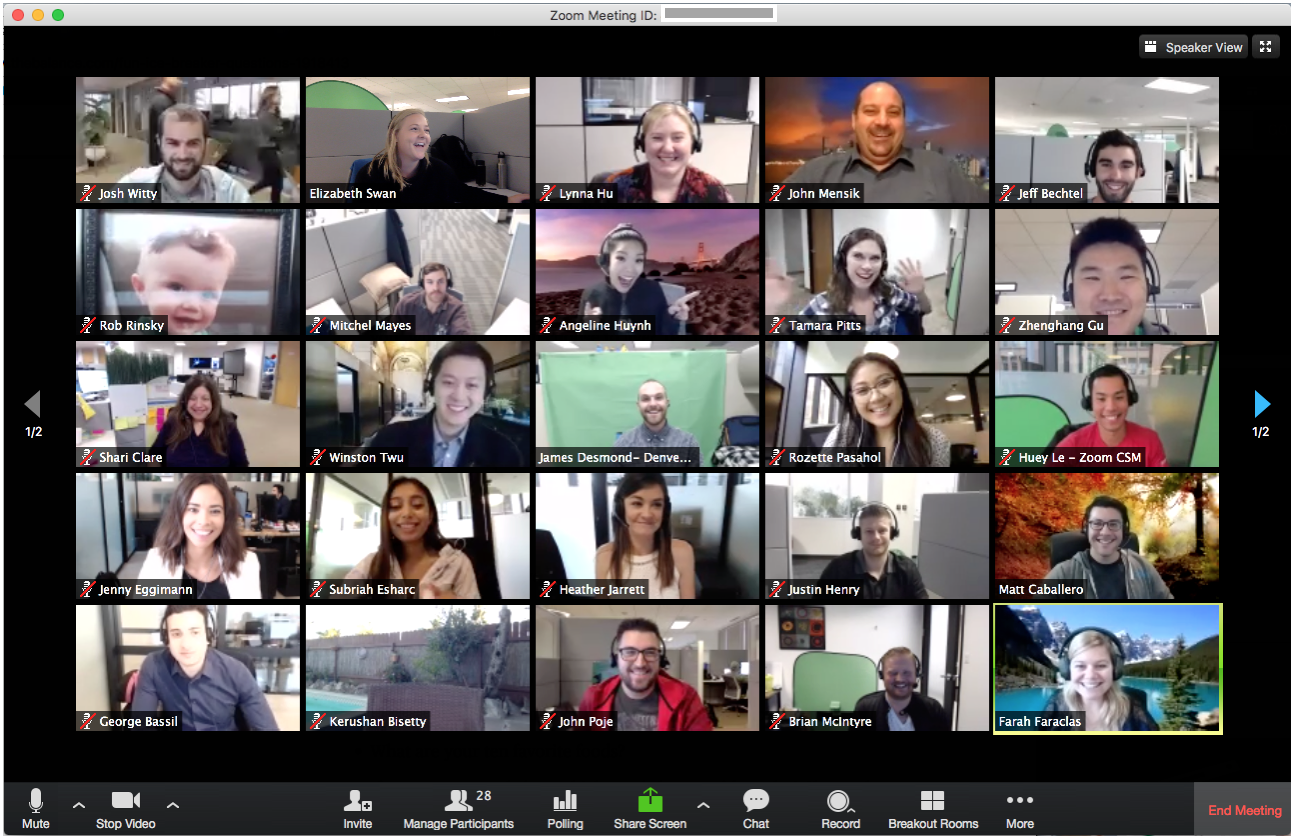
With so many these days resorting to virtual meetings, the use of Zoom video conferencing software has exploded. It emerged as the preferred platform to host anything from cabinet meetings to ballet classes.
Zoom reports usage shot up to 200 million daily users from an average of 10 million in December 2019, with an increase of 535% in daily traffic to its download page in the last month.
However, this sudden rise to a cornerstone communications channel for many also uncovered several privacy and security issues with this platform.
Some experts went as far as claiming that Zoom is malware, however this appears to be a far cry from fact. Simply put, Zoom is a legitimate and useful software which unfortunately is riddled with security vulnerabilities that were not previously submitted to such widespread scrutiny.
Here are the most critical issues reported:
- Zoom's privacy policymakes it possible to collect extensive data about its users — like videos, transcripts, and shared notes — and share it with third-parties for personal profit. On March 29, Zoom tightened its privacy policy to state that it shall not use data from meetings for any advertising.
- The attendee tracking feature, when enabled, lets a host check if participants are clicking away from the main Zoom window during a call. On April 2, Zoom permanently removed the attendee attention tracker function. A host of a Zoom meeting can, likewise, read private text messages sent during the call if it is recorded locally.
- Zoom's iOS app, like many apps using Facebook SDK, was found sending analytics data to the social network even if the user does not have a linked Facebook account. Later, this feature was removed.
- A flaw in Zoom's windows app made it vulnerable to UNC path injection' vulnerability that could allow remote attackers to steal victims' Windows login credentials and even execute arbitrary commands on their systems. Another bug allowed hackers to gain root privileges and access the mic and camera on macOS, thereby allowing for a way to record Zoom meetings. A patch was issued on April 2 to address these flaws.
- Zoom's claims that it uses end-to-end encryption to secure communications were proven to be misleading. The company stated that in a meeting where every participant is using a Zoom client and which is not being recorded, all sorts of content — video, audio, screen sharing, and chat — is encrypted at the client-side and is never decrypted until it reaches the other receivers. But if one of the value-add services, such as cloud recording or dial-in telephony, is enabled, Zoom has access to the decryption keys, which it currently maintains in the cloud. This also makes it easy for hackers or a government intelligence agency to obtain access to those keys.
- A practice named Zoombombing allows trolls to take advantage of open or unprotected meetings and poor default configurations to take over screen-sharing and broadcast porn or other explicit material. The FBI issued a warning, urging users to adjust their settings to avoid hijacking of video calls. Effective April 4, Zoom began enabling the Waiting Room feature(which allows the host to control when a participant joins the meeting) and requiring users to enter a meeting password to prevent rampant abuse.
In Zoom’s defence, is has swiftly and transparently responded to these and other flaws by issuing patches for identified flaws and shortlcomings.
In addition, the company has announced a 90-day freeze on releasing new features to "better identify, address, and fix issues proactively." It also aims to conduct a comprehensive review with third-party experts and release a transparency report that details information related to law enforcement requests for data, records, or content.
So ultimately, should you consider to or continue to use Zoom?
t would be easy to look at all of these flaws and say that people should simply stay away from Zoom. But it's not that straight forwrd.
Whilst the platform presents various severe security issues, we believe that choosing Zoom totally depends upon an individual's threat model (the practice of identifying and prioritizing potential threats and security mitigations to protect something of value, such as confidential data or intellectual property).
The most prominent security issues with Zoom appear to come from features deliberately designed to reduce enhance user experience during virtual meeting, which also inherently reduce privacy or security.
The most important takeaway for regular users is simply to think carefully about their security and privacy needs for each call they make. Zoom's security is likely sufficient if it is used for casual conversations or to hold social events and organize lectures.
For everything else that requires sharing sensitive information, there are more secure options like self-hosted Jitsi, Signal and Wire.
So, if you are worried about being Zoombombed, set a meeting password and lock a meeting once everyone who needs to join has joined. For more tips on how to make Zoom calls secure, check out the Electronic Frontier Foundation (EFF) guide to harden Zoom settings to protect your privacy and avoid trolls.